Видео с ютуба Identity Threat

Unlocking Identity Threat Detection & Response

Угроза стереотипов: беседа с Клодом Стилом

Identity Threat Detection and Response: Key Threat Metrics and Insights

Identity Threat Detection and Response (ITDR) | Streamline your identity protection

Identity Threat Detection & Response - on-prem to cloud ITDR from Microsoft

Modernize Your Identity Defense with Identity Threat Detection and Response (ITDR)

Identity Threat Protection and Okta Device Access - Logout

Social Identity Theory - Definition + 3 Components

What is Identity Protection?
Identity Threat Protection - SSF with Omnissa - Universal Logout

Обнаружение и реагирование на угрозы конфиденциальности | FortiSIEM

Identity Threat Protection - SSF with Omnissa - Okta Workflows

What is identity threat detection and response (ITDR)?

Identity Threat Detection and Response | Virtual Ninja Training with Heike Ritter

Identity Threats

Sophos ITDR - Identity Threat Detection and Response
Identity Control Plane Under Attack: Consent Abuse and Hybrid Sync Risks

What is an Identity Threat Assessment Framework and why we need one

IdentityTheft.gov Helps You Report and Recover from Identity Theft | Federal Trade Commission
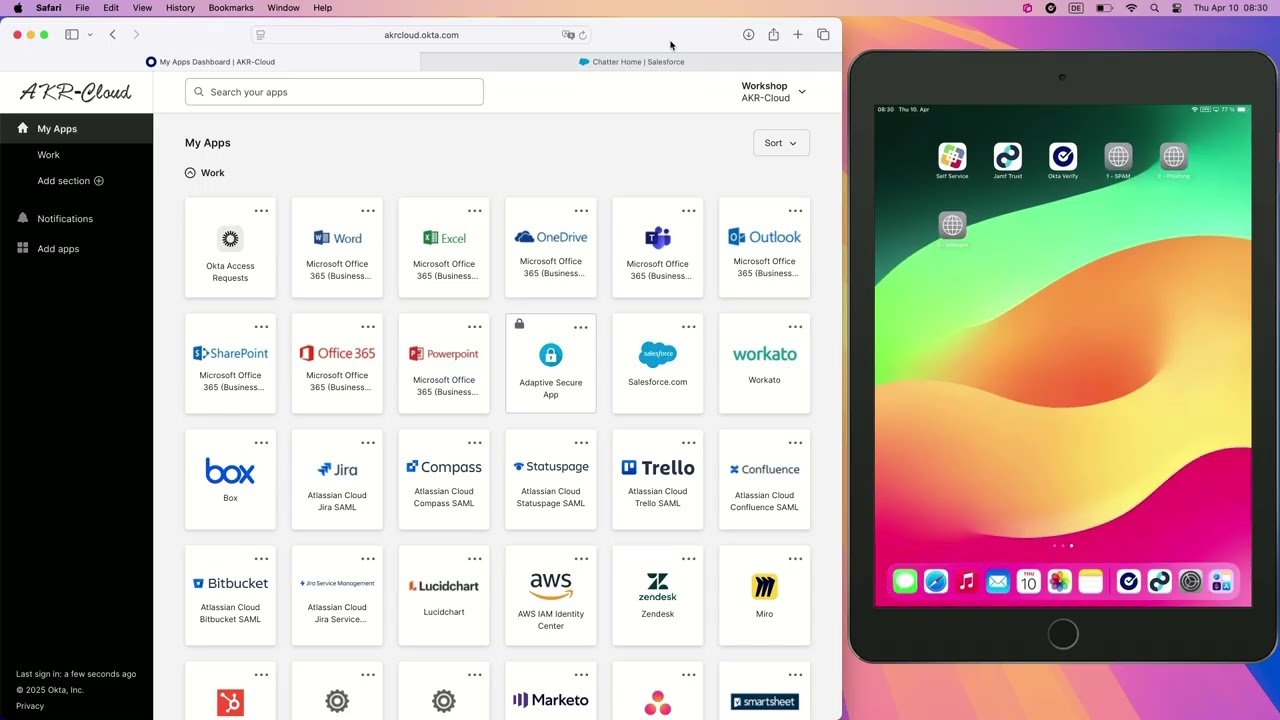
Okta Identity Threat Protection - Jamf SSF on mobile device